What you’ll do differently after this session
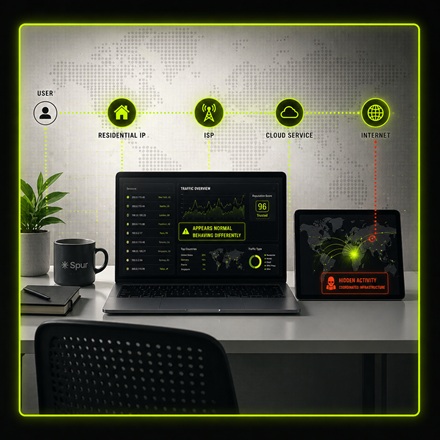
Most attacks now come from infrastructure that looks legitimate, including residential networks, mobile carriers, and cloud environments. That makes it harder to distinguish normal activity from real threats.
This session focuses on how to identify when a “clean” IP deserves a second look, and how better context changes detection and investigation outcomes.
- ■ Recognize when residential, mobile, or cloud IPs are masking attacker activity
- ■ Understand why IP reputation and “trusted” signals break down in modern environments
- ■ Distinguish normal user behavior from coordinated infrastructure abuse
- ■ Apply network-origin context in investigations without adding friction